A managing director of a large firm contacted us recently with a fairly major problem.
He received an email asking him to update his password and within seconds of obliging an email had been sent to his payments manager asking for a transfer to be made.
Never one to question the managing directors request, the payment was authorised. Moments later £10,000 had left the business account.
Meanwhile the managing director, who had sent no such email, could no longer access his Microsoft Office 365 email account and had rung us for advice.
Most people are familiar with phishing scams. These are email messages that pretend to be legitimate but instead infect your computer or harvest your passwords.
Some phishing scams are easy to avoid thanks to obvious grammatical errors or other red flags. Others, however, are so accurate they can even fool the experts.
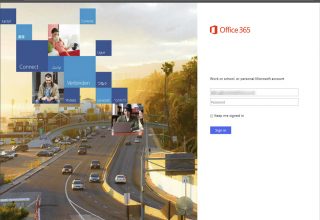
In this particular case, the spammer obtained the login credentials through Microsoft Office 365.
The hacker replicated the layout for the original Office 365 login page. This meant the managing director had entered his user name and password without question.
He would have only noticed there was a problem if he had closely examined the www address bar at the top on the page.
Instead he made a very costly mistake – one any one of us could have made.
There are systems to try and protect against this type of threat but technology evolves every day. As a result of this, we need to stay vigilant.
Perimeter security such as firewalls are essential, but next generation firewalls add additional security services and are even better.
On top of this, we would urge people to question everything.
We advise people to slow down, ready emails carefully, be wary of differing fonts or text size. As well as this, we advise hovering over hyperlinks in both emails and websites before you click them to check the destination address.
Never use the same email address and password combinations online, change your passwords periodically and keep them long and complex where possible using upper and lower case, numbers and symbols.
Use a password manager to store and generate secure passwords. Do not write passwords down and use two-factor authentication where possible.
When being asked to pay money to someone, we advise making a phone call to verify the details.
For more advice or information contact us.
“What impresses us most is their ability to convey the issue whilst avoiding the technical jargon that those outside of IT really don’t understand.”
- Jason Honey -